Online payment fraud is any unauthorized or manipulated card-not-present (CNP) transaction in which a fraudster attempts to extract value, goods, services, or funds without legitimate payment intent. But it isn’t just a loss problem. It’s an approval problem.
When fraud pressure rises, issuers and fraud systems tighten. That changes your authorization outcomes: more generic declines and more good customers blocked at the moment of purchase. The result is a three-part hit to unit economics: lower approval rates, higher dispute and chargeback ratios, and more pressure on your account health.
Fraud is also nearly universal. 98% of merchants reported experiencing at least one type of fraud in the past 12 months. The same report found that 14% of merchants reported false positive rates above 10% on disputed e-commerce orders. It’s a signal of how often legitimate activity gets misclassified when risk posture tightens.
The hard part is that you pay in losses and chargebacks if your fraud controls are too loose. However, you may also end up paying for false declines if your approval controls are too strict, and that revenue doesn’t come back on its own.
This guide breaks down the main types of online payment fraud, where they show up in the payment flow, and how to control fraud without quietly killing approvals. And because even well-calibrated risk systems still decline legitimate customers, we’ll close with how to recover those transactions safely.
What is online payment fraud?
Online payment fraud is an unauthorized or manipulated card-not-present (CNP) transaction in which a fraudster attempts to extract value (goods, services, or funds) without legitimate payment intent.
True unauthorized fraud involves a bad actor using stolen or compromised credentials without the cardholder's knowledge. In contrast, chargeback fraud is a disputed transaction in which the cardholder contests a charge they authorized, typically to obtain a refund while retaining the goods or services.
Merchants lose money through two distinct mechanisms, both of which affect revenue but require different responses:
- Direct losses include chargeback fees, lost merchandise, and card network fines when chargeback thresholds are breached.
- Indirect losses accumulate through fraud controls. When risk thresholds tighten, false decline rates climb, and good customers are blocked at authorization, turning attempted purchases into failed payments.
Fraud can enter the online transaction lifecycle at multiple points: before authorization, at authorization, or after fulfillment. Knowing where fraud enters the flow determines how you control it, and also helps you ascertain whether you are dealing with unauthorized CNP fraud driven by bad actors, or chargeback fraud initiated by cardholders who received their goods but dispute the charge anyway.

The main types of online payment fraud merchants face
1. Unauthorized payment fraud (true CNP fraud)
- Stolen card/credential use involves a fraudster using card data obtained through breaches, phishing, or dark web purchases to complete a CNP transaction. The legitimate cardholder is unaware until a statement review or bank alert triggers a dispute.
- Card testing/carding is the automated process of validating stolen card credentials by running low-value transactions (sometimes fractions of a cent) before using valid cards for higher-value fraud. Velocity spikes are the primary fraud signal generated.
2. Account and identity fraud
- Account takeover (ATO) occurs when a fraudster gains access to a legitimate customer account through credential stuffing, phishing, or brute force, then uses stored payment methods to transact. Brand impersonation and website cloning are common inputs to ATO because they drive credential theft at scale. It's difficult to detect because the card credentials are valid and the account history looks clean.
- Synthetic identity/new account fraud involves constructing a fictitious identity using a mix of real and fabricated data, which is often a real Social Security number with a false name and address. Fraudsters open credit card accounts using that synthetic identity to establish a credit file before defaulting or cashing out.
3. Post-transaction abuse (disputes and refunds)
- Friendly fraud/chargeback abuse is a first-party fraud pattern in which a cardholder completes a legitimate transaction, receives the goods or services, and then files a dispute claiming non-delivery or unauthorized use. It's the most operationally expensive fraud type for online merchants because it is often difficult to distinguish from a legitimate dispute at the point of claim without strong supporting evidence.
- Refund and returns abuse includes “item not received” claims, empty-box returns, and wardrobing, which is the practice of purchasing items for temporary use before returning them. It bypasses the card network dispute process but produces the same revenue loss for the merchant.
4. Incentive and policy abuse
- Promo/coupon/loyalty abuse involves exploiting discount codes, referral programs, or loyalty point structures through multi-accounting or automation to extract value beyond program intent.
- Free-trial and subscription abuse is the pattern of creating multiple accounts, often with disposable emails and prepaid cards, to cycle through free trials or promotional pricing without converting to paid status.
5. Fulfillment and networked fraud patterns
- Triangulation fraud occurs when a fraudster takes orders on a fake storefront, uses stolen cards to fulfill them from a legitimate merchant, and pockets the payment.
- Reshipping and mule behavior involves fraudsters shipping goods purchased with stolen cards to a recruited intermediary, known as a mule. The mule repackages and reships them to the fraudster to conceal the origin of the transaction.

Card-not-present (CNP) fraud vs. chargeback fraud: Key differences
This table maps the key differences between unauthorized CNP fraud and chargeback fraud, so you can identify which problem you are dealing with and respond accordingly.
Where fraud shows up in the payment flow
Online payment fraud is really multiple failure modes distributed across the transaction lifecycle. If you don't identify where in the flow a fraud event occurred, you end up treating every signal the same way, which means either approving too much and absorbing losses, or blocking too much and creating false declines.
Here is how fraud maps across each stage of the payment flow:
- Checkout – The customer initiates a transaction. Pre-checkout fraud, such as ATO and synthetic identity fraud, has already occurred by this point, at the account layer before purchase intent is expressed.
- Risk screening – The merchant's fraud stack evaluates the transaction. Card testing and bot-driven credential validation target this stage with high-volume, low-value probes.
- Authorization request – The transaction is submitted to the issuer. Stolen card CNP fraud is attempted when the fraudster submits valid stolen credentials, and the issuer’s risk model is the primary gatekeeper at authorization.
- Issuer decision – The issuer approves or declines based on its risk model and the signals the transaction carries. Conservative risk models and incomplete transaction signals produce false declines on legitimate transactions at this stage.
- Capture and fulfillment – Once authorized, the merchant captures the payment and fulfills the order. This stage is where operational controls and fulfillment confirmation matter most, especially for post-transaction disputes, refund abuse, and delivery claims.
- Settlement – Funds move through the card network to the merchant’s acquirer/processor (and then to the merchant, depending on their setup). Unresolved disputes initiated post-settlement result in funds being pulled back via the chargeback process.
- Post-transaction disputes and refunds – After fulfillment, friendly fraud and refund abuse enter the payment flow when the cardholder files a dispute or makes a false return claim.
Checklist: How to control online payment fraud
Follow these steps to control online payment fraud across the full transaction lifecycle:
✅ Start with bot and card-testing controls
Bot and card-testing attacks generate large volumes of low-value authorization attempts in short windows. They degrade signal quality across your entire fraud stack, inflate decline rates, and, when left unchecked, contaminate the data that issuers and fraud models use to make future decisions on your transactions. Controlling for bots early protects the integrity of everything downstream.
How to do it:
- Set velocity rules that trigger friction or block on high-frequency, low-value authorization patterns across shared card attributes such as BIN, IP, and device fingerprint.
- Monitor authorization attempt rates in real time. A spike in sub-threshold transactions is a reliable early signal of a carding attack.
✅ Improve signal quality to reduce false positives
Issuers authorize based on the signals your transaction carries, plus issuer-side context and real-time risk posture. Thin, inconsistent, or incomplete data increases the probability of a conservative ”no,” even for a legitimate customer. Better signals produce improved outcomes at authorization without requiring rule changes on your end.
How to do it:
- Ensure AVS data is consistently passed, and include CVV when it’s available for customer-initiated entry (CIT), since missing fields can be treated as risk indicators by many issuers.
- Pass 3DS data where applicable, because authenticated transactions can increase issuer confidence and may shift liability depending on the authentication outcome and scheme rules.
- Enrich transaction metadata with device fingerprinting and behavioral signals to give your fraud stack and the issuer a more complete picture.
✅ Use tiered risk policies instead of one global rule set
A single global fraud threshold applied across all transaction types, geographies, and customer cohorts over-blocks in low-risk scenarios and under-blocks in high-risk ones. Tiered policies let you calibrate risk tolerance to the actual profile of each transaction segment, which reduces false declines without increasing fraud exposure. Implementing them starts with a security risk assessment of your highest-loss fraud patterns and your highest-cost false-decline cohorts.
How to do it:
- Segment fraud rules by channel (mobile vs. desktop), geography, product type, and customer tenure.
- Apply higher friction selectively where risk signals are elevated but not conclusive. Use a 3DS step-up or manual review before defaulting to a decline.
- Review and recalibrate fraud thresholds on a regular cadence because fixed configurations lose accuracy as fraud patterns evolve.
✅ Monitor the right metrics: Approval rate and false-decline indicators
In payments, conversion is not checkout completion; it is authorization through settlement.
Most fraud reporting focuses on the chargeback rate and fraud loss. However, by the time those metrics reflect a problem, revenue has already been lost.
The metrics that reveal whether your controls are correctly calibrated are the authorization rate by decline code, false positive rate on disputed orders, and the proportion of your decline volume that consists of generic ”do not honor” responses. The same issue exists upstream in reporting: AI-era marketing attribution recommendations are pushing teams to be stricter about which events are treated as conversions, which is exactly why decline-code hygiene matters.
How to do it:
- Track authorization rate segmented by decline code to distinguish recoverable soft declines from hard stops.
- Flag any increase in ”do not honor” volume as a signal that your fraud posture may be tightening beyond what the transaction risk warrants.
- Review false positive rates on disputed orders regularly. If legitimate transactions are being blocked at authorization, your thresholds need recalibration.
✅Have a recovery plan for inevitable false declines that doesn’t increase your fraud exposure
Even well-calibrated fraud controls will produce false declines. That is why you need a recovery plan, a defined process for identifying eligible declined transactions and converting them into successful payments.
Having one is crucial because that revenue does not come back on its own, but the recovery process itself must not push additional fraud exposure back onto your own merchant accounts.
How to do it:
- Define eligibility criteria for declined transactions that are candidates for recovery by decline code, amount, geography, or customer cohort, and route only those transactions to a recovery process.
- Ensure recovery happens at the processing layer and not the checkout layer, so customers are not asked to re-enter details or take additional steps.
- Use a recovery solution like Paymend that operates on separate infrastructure from your own merchant accounts, assumes full liability on any disputed transaction it processes, and requires no changes to your checkout flow.
When fraud controls create false declines: Recovering revenue safely
Online fraud controls are built to minimize loss, so they often win by declining. The problem is that in card-not-present (CNP) transactions, conservative rules and issuer risk models also block good customers, which shows up for merchants as false declines and lost revenue.
A false decline is a conversion leakage at authorization that occurs because:
- CNP is a low-visibility environment where issuers default to ”no” when signals are weak.
- Fraud spikes cause temporary risk tightening that catches legitimate transactions.
- Safety controls configured globally get over-applied to segments where the risk does not warrant them.
You can reduce false declines by improving signal quality and segmenting risk policies, but you’ll never drive them to zero. That’s why recovery needs to be operationalized as a payments-layer capability, not treated as a one-off exception process.
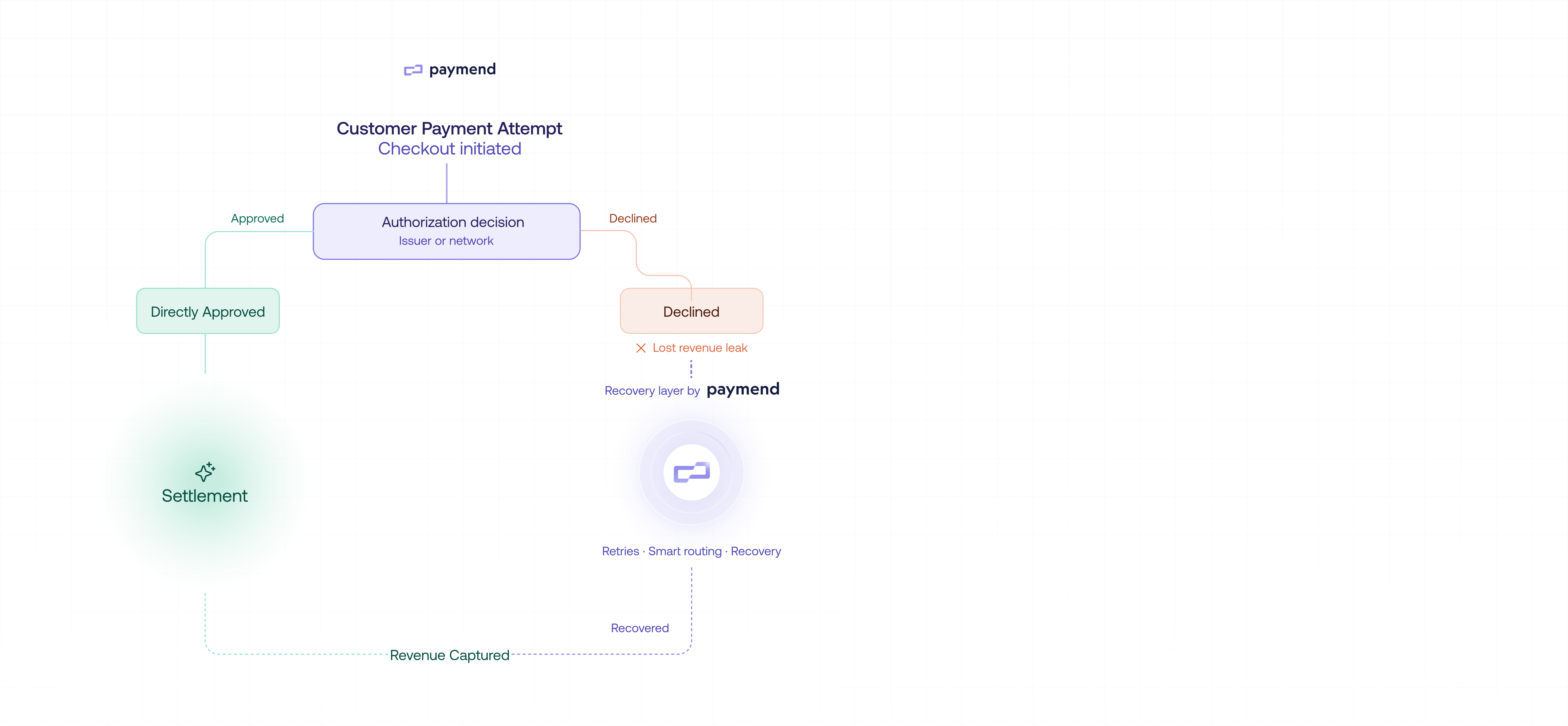
It’s best to use a revenue recovery platform like Paymend that focuses on declined card transactions and converts eligible declines into approvals by retrying payments on its own infrastructure. It maintains a full-liability model for transactions it processes on Paymend’s own merchant accounts, so the fraud exposure is not shifted to the merchant’s accounts. There’s no checkout disruption and no added buyer steps, and the platform only earns on recovered revenue under its “no-win, no-fee” model.
Control fraud. Protect approvals. Recover what slips through.
Online payment fraud means more than just lost revenue. It changes issuer and fraud posture, and the side effect is often lower approvals for legitimate customers. But fraud controls that over-correct create hidden revenue leakage at authorization, inflating CAC and depressing conversion even when demand is strong.
When your fraud posture creates false declines, the question becomes how to recover eligible declines safely without increasing fraud exposure on your own merchant accounts.
For many merchants, the answer is Paymend, a full-liability revenue recovery platform that converts declined card transactions into successful approvals by retrying them on its own infrastructure.
Paymend helps merchants recover eligible declined card transactions without increasing fraud exposure on your own merchant accounts. Paymend retries declines on its own infrastructure and assumes full fraud liability for the transactions it processes. Recovery happens behind the scenes with no checkout disruption and no added buyer steps. You control what traffic gets sent, and Paymend can reject high-risk transactions before they enter recovery. Book a demo to see how Paymend recovers eligible declined transactions from your fraud controls.


















